CYBER INCIDENT RESPONSE SOFTWARE
Respond to breaches fast with the iCONECT cyber incident response platform.
When a breach event happens, those impacted need to know as soon as possible. iCONECT helps you identify and extract the critical information you need from unstructured data, so you can develop a comprehensive incident response plan and notification list.
Schedule your demo today.
Data teams everywhere love using iCONECT.
Hard-won experience. Innovative technology. Responsive support.
iCONECT brings everything to the table.
+
Years in Business
B+
Number of Documents Processed
$
M+
ROI Savings Delivered
Cyber incident response software with a touch of GenAI
iCONECT uses GenAI to deliver the right tools for each dataset, precisely when you need them to ensure complete transparency and clarity without relying solely on automated systems:
- PII Identification: Bulk-select documents and send them to your model of choice, including those from OpenAI, Microsoft, and Google
- OCR/ICR Text Extraction: Convert printed and handwritten documents into searchable, editable digital text for fast investigations
- Normalization: Develop a deduplication process to create an efficient notification list
Get notified faster. Respond better.
In a data breach crisis, immediate action and transparency are non-negotiable. iCONECT’s cyber incident response software swiftly identifies and extracts the critical PII locked within unstructured data, allowing you to instantly deploy a comprehensive incident response plan and notify every affected party. iCONECT provides robust features and tools designed to accelerate your workflow while ensuring precision in your findings.
Identification
iCONECT uses a mix of search terms, regular expressions and AI reviews to efficiently identify personal information within documents. You can also minimize data through iCONECT’s deduplication and threading capabilities to improve accuracy.
Reporting & Extracting
Reporting and extracting data that matches defined triggers is easy and intuitive, thanks to iCONECT’s automation. Whether you are a base reviewer or a power user, you can use iCONECT to report and extract information without ever having to type.
Verification
iCONECT enables users to define their criteria, so you can verify results manually or automatically. iCONECT enhances the validation process by providing more screen space and presenting the data in a unique format compared to other tools.
Normalization
Create a notification list by deduplicating and normalizing the extracted elements. iCONECT offers sophisticated grouping capabilities and transparency in match logic, providing clarity and confidence in the matching process.
The iCONECT Advantage
- World Class Support
- Secure Deployment
- Visible Match Logic
- Ongoing Platform Development
- Purpose-Built Software
- Stable Brand
-
World Class Support
When data is compromised, you need a dedicated team by your side to help you through the response process. iCONECT is here to support you 24/7. 
-
Secure Deployment
Whether you prefer SaaS or on-premises deployment, iCONECT offers a multi-layered security program with SOC2 certification, regular security training, penetration testing, and careful development to protect your data. All solutions include strong workstation and server security, rigorous data protection protocols, and controlled access, backed by our rapid-response security experts. 
-
Visible Match Logic
Transparent matching logic means you can see if there are potential matches for any individual, limiting the amount of quality control required. 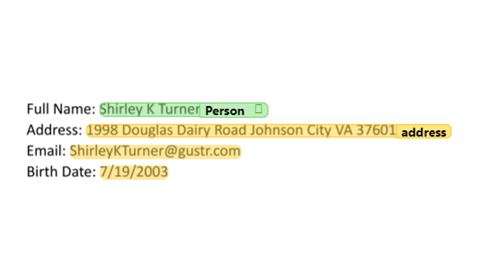
-
Ongoing Platform Development
iCONECT is a platform committed to continuous improvement. Our feature development is driven by a constant focus on problem-solving. 
-
Purpose-Built Software
Industry experts helped build iCONECT. Using focus groups and personal connections, we developed our software to address your pain points directly. 
-
Stable Brand
iCONECT has been around since 1999, and we’re not going anywhere. That means you can actually rely on our experienced team to meet all your cyber data mining challenges head on, today and well into the future. 
Make the right move with the right cyber incident response software.
Take the first step toward better incident response with iCONECT.